Introduction: The Value of Privacy in the Digital Age
In an increasingly connected world, the Internet has become the primary space for the exchange of ideas and personal expression. Every day, billions of people use the network for work, communication, shopping, gaining information, and much more. However, this incredible resource has also brought new challenges in terms of privacy and data security. Each time we browse the web, we leave behind a digital footprint that can be collected, analyzed, and in some cases, exploited. Companies, governments, and malicious actors can use this information for a variety of purposes, not always in the best interest of individuals.
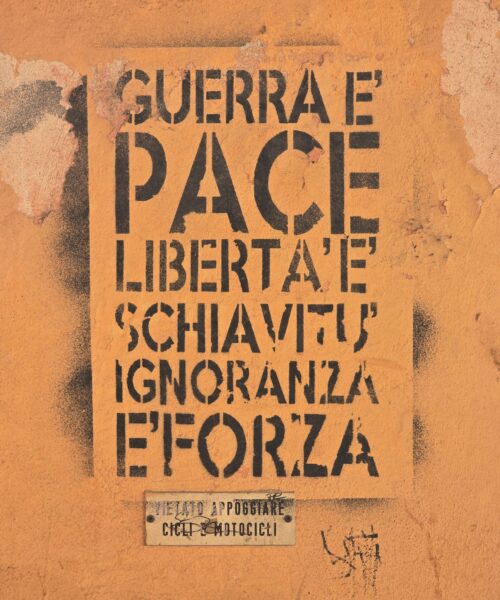
In this context, online privacy is not just a matter of protecting personal data, but a fundamental right that can impact our freedom of expression, our security, and in some cases, even our survival. If we fear that our communications are being monitored, we may hesitate to voice our opinions, seek information on sensitive topics, or connect with others. This is particularly true for those living under oppressive regimes, where freedom of expression can be severely limited and mass surveillance is the norm.
What is TOR? An Acronym for Freedom
This is where TOR comes into play, an acronym for “The Onion Router,” an open-source software that allows users to browse the Internet anonymously. Originally developed by the United States Navy to protect government communications, TOR is now available to anyone who wishes to shield their online identity. Utilizing a series of servers, or nodes, TOR “bounces” a user’s traffic through multiple locations around the globe, making it extremely difficult for anyone monitoring the network to determine who the user is or where they are coming from. But, as we’ll see, TOR is much more than just a simple tool for ensuring online anonymity: it has become a bulwark of freedom of expression and a shield for those living under totalitarian regimes.
TOR exploits a series of servers, known as nodes, through which the user can route their connection, thereby creating a cryptic and hard-to-trace path. Each node knows only the previous and next node in the chain but has no information on the identity of the end user. This method, called “layered routing” (hence the name “onion”), ensures a high level of anonymity.
For dissidents and activists living in countries with authoritarian governments, TOR can be a real lifeline. These individuals are often under constant surveillance and can face severe consequences if caught criticizing the government or organizing protests. By using TOR, they can communicate securely with others, disseminate information abroad, and access news and resources that might be blocked in their own country.
Thus, while surfing the Internet may often seem like a benign everyday activity, for many around the world, it’s an act of resistance. TOR is a vital tool that protects the anonymity of these individuals, allowing them to fight for their rights and freedoms without fear of persecution.
TOR in Authoritarian Countries: A Light in the Darkness of Censorship
But how does this translate into a safeguard for dissidents in dictatorial countries? In these contexts, the free expression of ideas can carry severe risks, ranging from legal persecution to detention, and even torture. TOR provides these individuals with a secure channel through which they can communicate their ideas, gather and disseminate information without fear of being identified and persecuted.
In countries with authoritarian regimes such as China, Iran, and Russia, internet access is tightly controlled and censored by the government. This control can include monitoring citizens’ online activities, censoring content deemed unsuitable or threatening to the regime, and in some cases, completely shutting down access to certain social media or news platforms.
This control over digital freedom creates an environment of fear and self-censorship, where people are reluctant to express their opinions for fear of repercussions. This is where TOR comes into play; with its powerful anonymity tool, it allows users to circumvent these restrictions and censorship.
During the 2009 protests in Iran, for example, authorities had blocked access to numerous social media platforms in an attempt to stifle communication among protestors and the spread of news about the protests abroad. Thanks to TOR, activists were able to coordinate their actions, share vital information, and disseminate news about the protests outside of Iran.
TOR allowed activists to maintain anonymity, reducing the risk of being identified and persecuted. Moreover, it enabled journalists and reporters to provide the world with an accurate account of what was happening, despite the Iranian government’s efforts to control the narrative.
Similarly, in China and Russia, where the governments tightly control and censor internet access, TOR continues to be an essential means for activists, journalists, and dissidents to share information, communicate, and organize actions, while maintaining anonymity.
The Limits of TOR: Not a Panacea, but an Essential Tool
While TOR offers a significant level of protection, it’s crucial to remember that it’s not a universal solution for all privacy and security issues online. Even when used correctly, TOR can’t guarantee complete anonymity. Sophisticated users or actors with significant resources could, theoretically, exploit weaknesses in the system or use advanced attacks to trace TOR users. For instance, if a user accesses an unencrypted website through TOR, an adversary might be able to see what they are doing on that site.
Moreover, using TOR can draw attention from certain surveillance bodies or authorities. In some countries, using TOR is considered suspicious and could lead to further investigation. Users need to be aware of these risks and take all possible measures to protect their privacy, such as using encrypted HTTPS connections and avoiding the provision of personal information.
Finally, like any technology, TOR can be used for both benevolent and malicious purposes. While many use TOR to protect their privacy, others may exploit the network’s anonymity for illegal activities. This has led to debates and critiques about the responsibility and regulation of TOR.
Nonetheless, despite these limitations and challenges, TOR remains a potent tool for the defense of human rights and freedom of expression. Its capabilities to provide a significant degree of anonymity and to circumvent censorship are essential for many activists, journalists, and dissidents worldwide. In an era where mass surveillance and censorship have become increasingly pervasive, TOR offers a glimmer of hope for those fighting for freedom of speech and the right to privacy.
Criticism of TOR: The Shadow of Online Crime
While serving as a potent resource for the defense of human rights and freedom of expression, TOR has faced numerous criticisms for its ability to provide a haven for criminal activities online. Indeed, the very privacy and anonymity that TOR offers its users can be, and often is, exploited by those seeking to conceal illegal or ethically questionable behavior.
Illegal activities on TOR range from the sale of illicit substances, to arms smuggling, to the distribution of copyrighted material, or the spread of pornographic content. Because of this, TOR is often associated in the media and popular imagination with the darker corners of the web, commonly referred to as the “Dark Web” or “Deep Web.”
This situation has led to a series of debates about the responsibility of TOR’s creators and operators. Should they be held accountable for the illegal activities conducted on their platform? Should they take steps to prevent or limit such behavior?
TOR’s developers argue that the primary goal of their network is to ensure privacy and freedom of expression. While acknowledging that their platform can be abused, they maintain that they cannot be held responsible for the actions of individual users. They further argue that the legitimate and positive uses of TOR far outweigh the illegal ones.
Despite these criticisms and challenges, TOR’s mission to provide a means for online anonymity and freedom of expression is more critical than ever. In an era where online privacy is increasingly at risk, and where dissidents and activists must struggle against censorship and surveillance, the need for tools like TOR can only grow.
Conclusion: TOR, More Than Just a Technological Tool
The TOR network represents much more than a mere technological convenience; it is a beacon of freedom that shines in the often engulfing darkness of oppression. Designed to protect the anonymity and privacy of its users, it has gained fundamental importance in the global landscape of human rights advocacy.
It provides a shield of anonymity to those who need it the most—dissidents, journalists, human rights activists—who live in countries where freedom of speech is stifled and privacy is invaded.
TOR faces significant challenges, such as its use for illegal activities and subsequent public scrutiny. However, despite these criticisms, its core value and positive potential as an instrument of freedom and resistance remain unaltered.
The current digital age is marked by an increasing erosion of online privacy, with governments and private companies gathering and using personal data in unprecedented ways. In this context, the need and relevance of tools like TOR, which can protect individuals’ anonymity and privacy, are set to increase.
In conclusion, the story of TOR is a powerful testament to the importance of privacy and anonymity on the internet. It reminds us that technology can be a double-edged sword, capable of fueling both freedom and oppression. But most importantly, it reminds us that, even in the darkest times, there are tools and people committed to defending freedom, resisting against oppression, and promoting human rights.
Final Reflections: Continuing to Look Forward
The TOR network continues to evolve, and we, along with millions of users worldwide, will keep a close eye on this evolution. TOR stands as a bastion of freedom in the digital age, a lifeline for many who live under repressive regimes.
Our aim, like that of TOR’s developers and users, remains the same: to safeguard and uphold the fundamental rights of every individual—the rights to privacy and freedom of expression. These rights, enshrined in the United Nations’ Universal Declaration of Human Rights, should be guaranteed to everyone, no matter where they live.
Looking ahead, the significance of TOR and similar tools will likely only increase, given the rise of digital surveillance and censorship by governments around the world.
However, like any technology, TOR is not immune to abuse. Its capacity to offer anonymity has, regrettably, also led to illicit uses, which should never overshadow the network’s core importance in protecting human rights.
We therefore conclude with a call to responsibility and vigilance. It is our duty as digital citizens to use tools like TOR wisely and responsibly, always remembering that our fight for privacy and freedom of expression is, ultimately, a fight for human rights—a fight worth waging, now and always.